depthfirst reasons through your application to find real attack paths, including business logic flaws and chained vulnerabilities that only emerge from understanding how your code works.
Security starts with understanding your app
Connect your codebase. depthfirst maps your entire application. Multiple LLMs run in parallel, spending hours per repository to build a structural understanding of how your system works.
-
-
depthfirst evaluates the conditions required for exploitation and runs a dynamic test against your running application. Only findings that can actually be triggered reach your queue.
-
depthfirst generates a pull request for every confirmed vulnerability, written against your actual codebase and conventions. Developers review and merge without leaving their workflow.
-
depthfirst replays the same attack after every fix is merged. A vulnerability is resolved only when exploitation fails in your running application, not when the code changes.
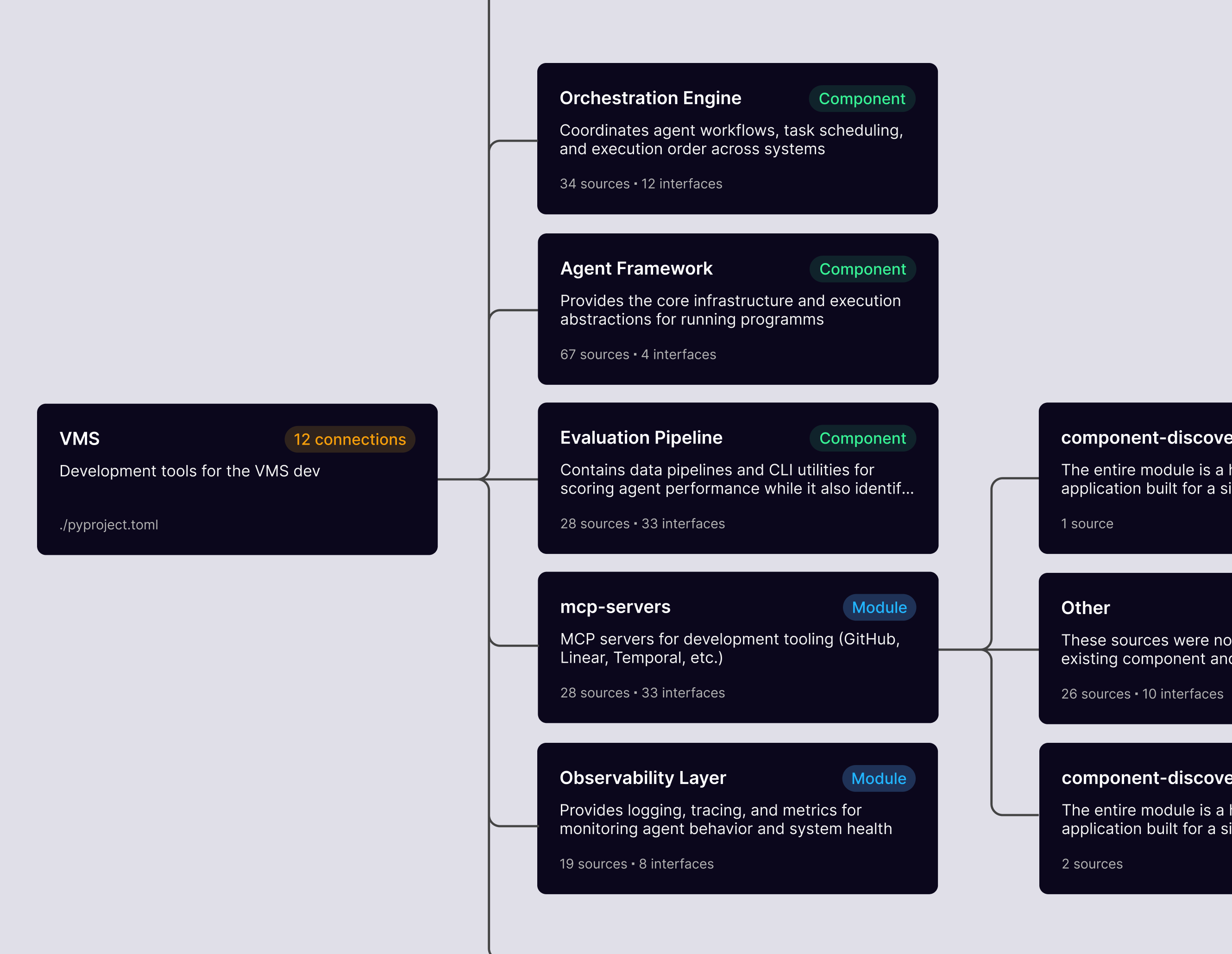
The component graph
depthfirst maps data flows, cross-service relationships, and every dependency across your repositories. Every finding is grounded in how your system actually works.
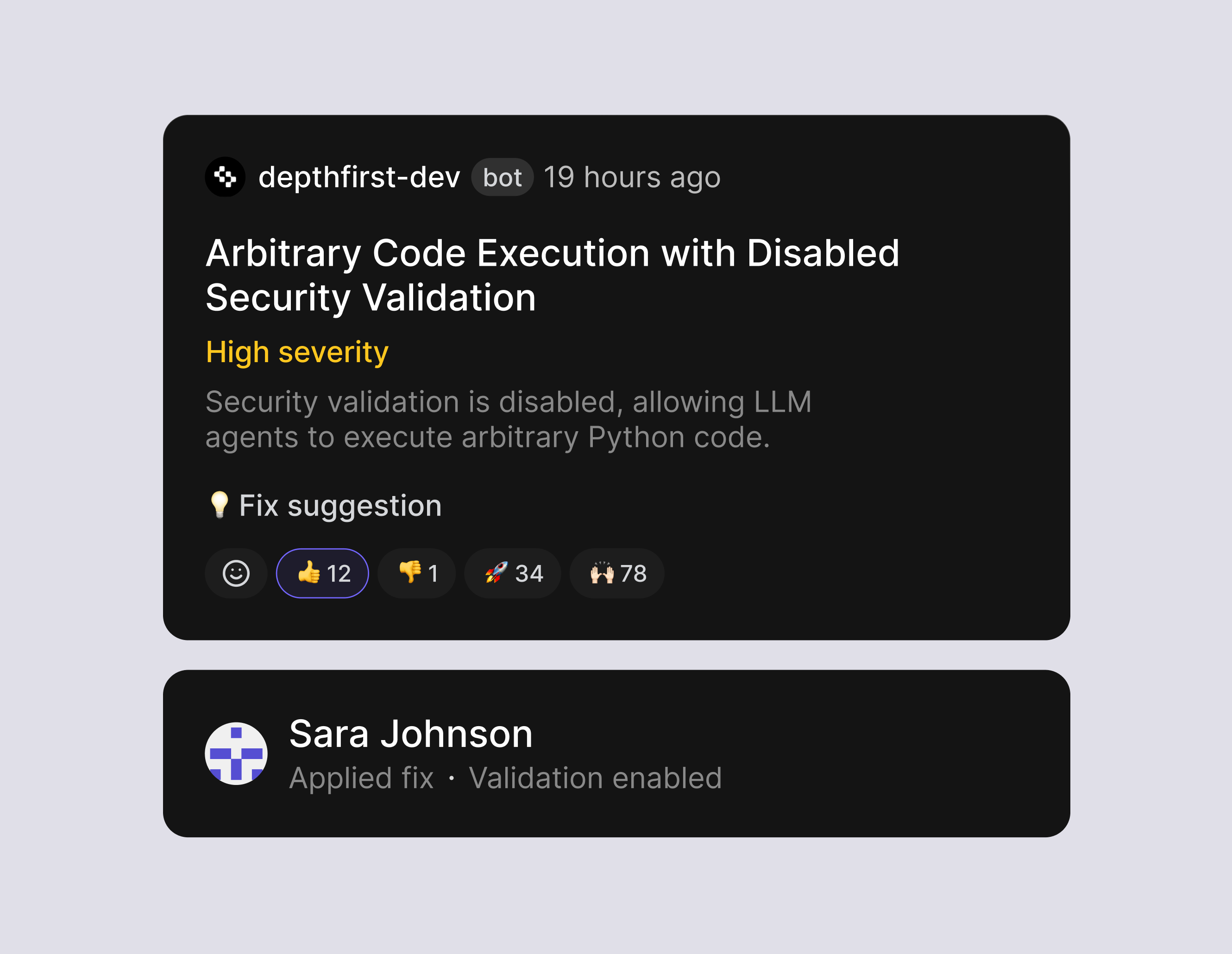
Continuous learning
depthfirst improves over time by learning from developer feedback on its recommendations. Adjustments are visible on the platform so you can track what the system has learned.
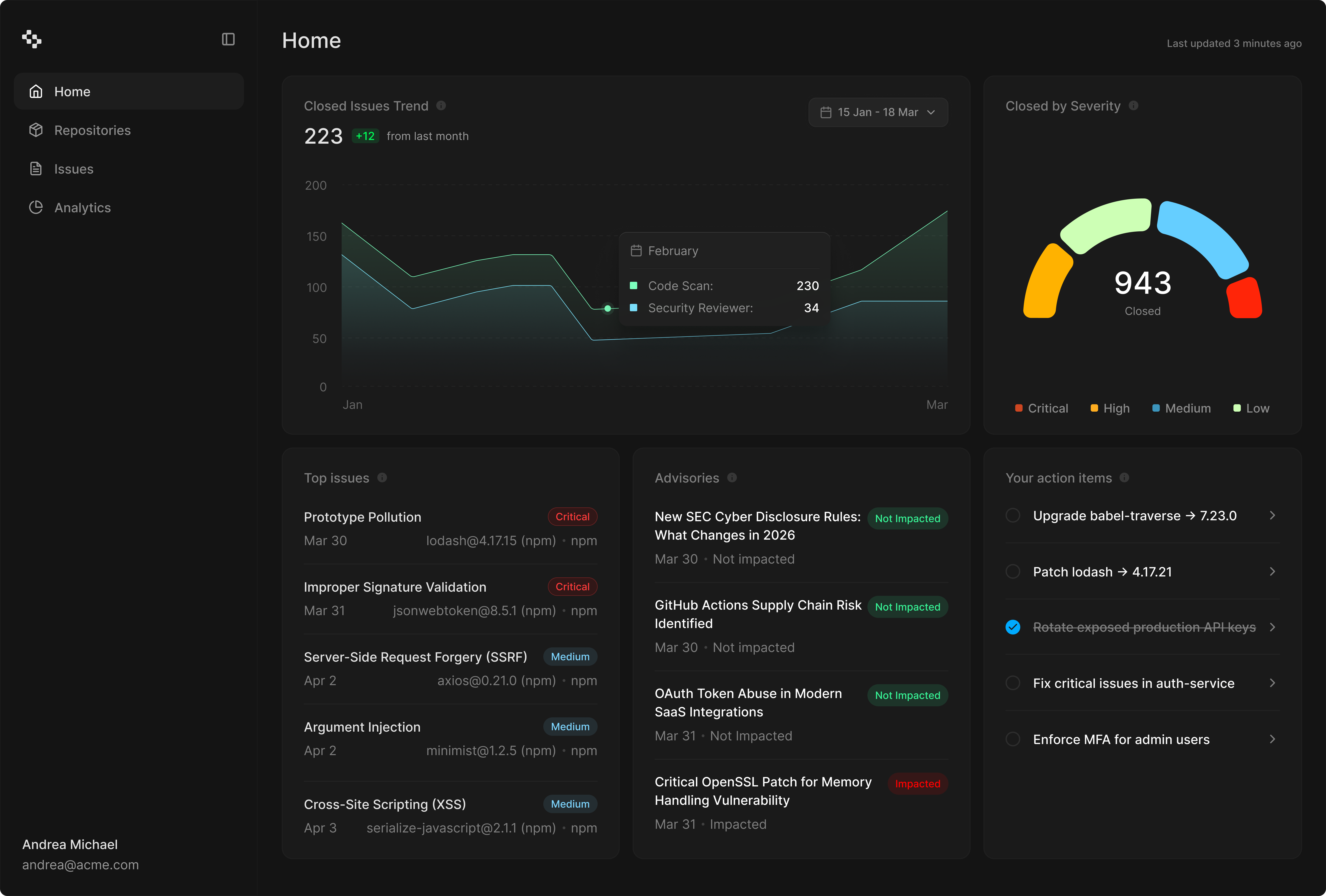
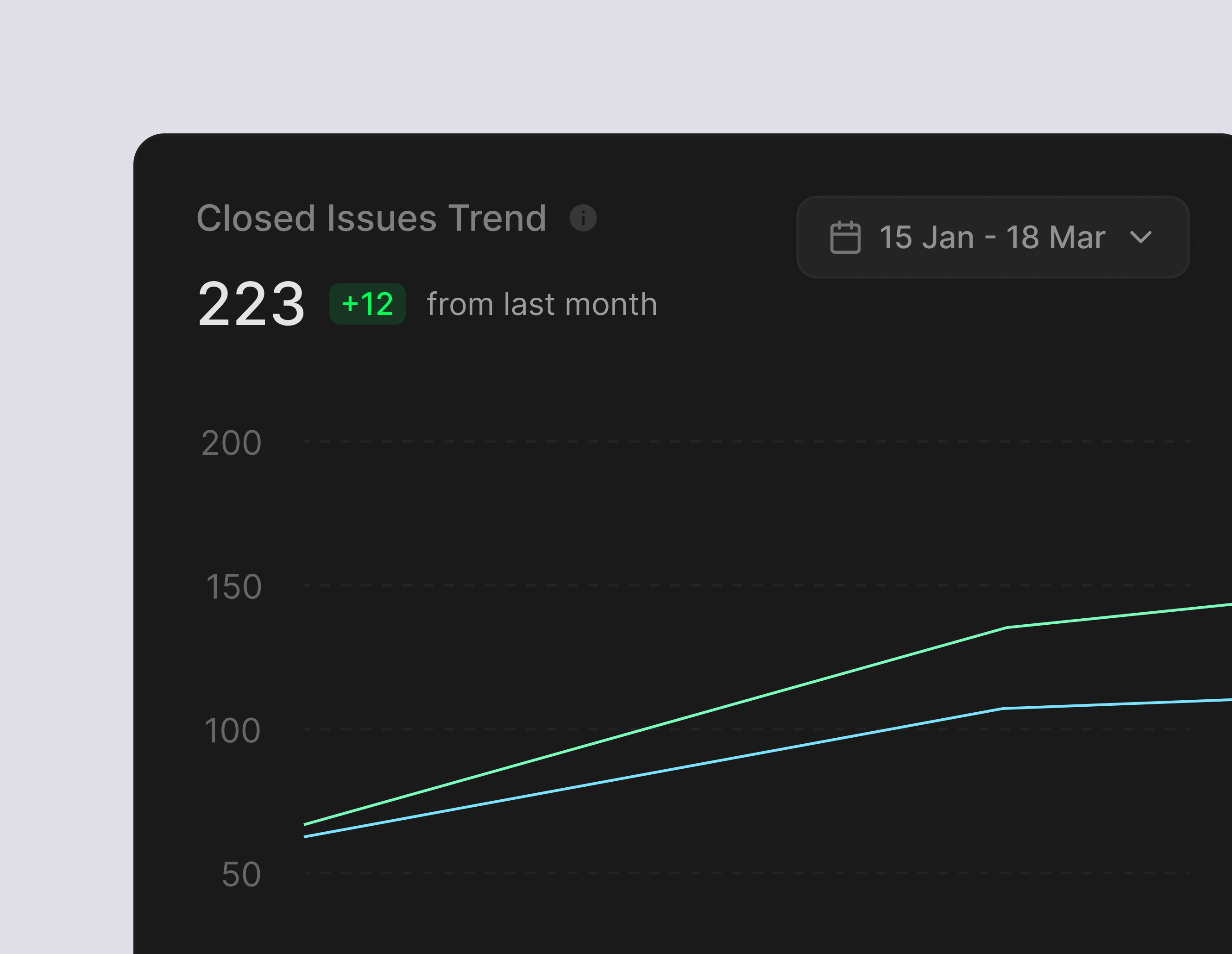
Security analytics
Track active vulnerabilities by repository and severity, monitor your burn down, and measure time to remediate. Full visibility across every repository in one place.
Business context
Add context about each repository in plain language: what the service does, who uses it, and what it handles. Findings adjust to reflect your actual risk profile.
Natural language rules
Write detection rules in plain English and depthfirst applies them across your codebase.
API Connectivity
Query findings, trigger scans, and integrate depthfirst into your own workflows and tooling programmatically.
Code
Find real vulnerabilities by tracing business logic, data flows, and cross-service interactions across your codebase.
Supply Chain
Trace risk through your full dependency tree and surface only the vulnerabilities with a real execution path to them.
Secrets & Sensitive Data
Detect and validate credentials across your codebase, CI/CD pipelines, and runtime environments.
Dynamic Testing
Confirm which vulnerabilities are exploitable by testing your running application with real attack paths.