Tests whether AI-powered features execute injected instructions by manipulating inputs across user-facing and backend prompts. Findings show the injection path and model response.
Dynamic Testing
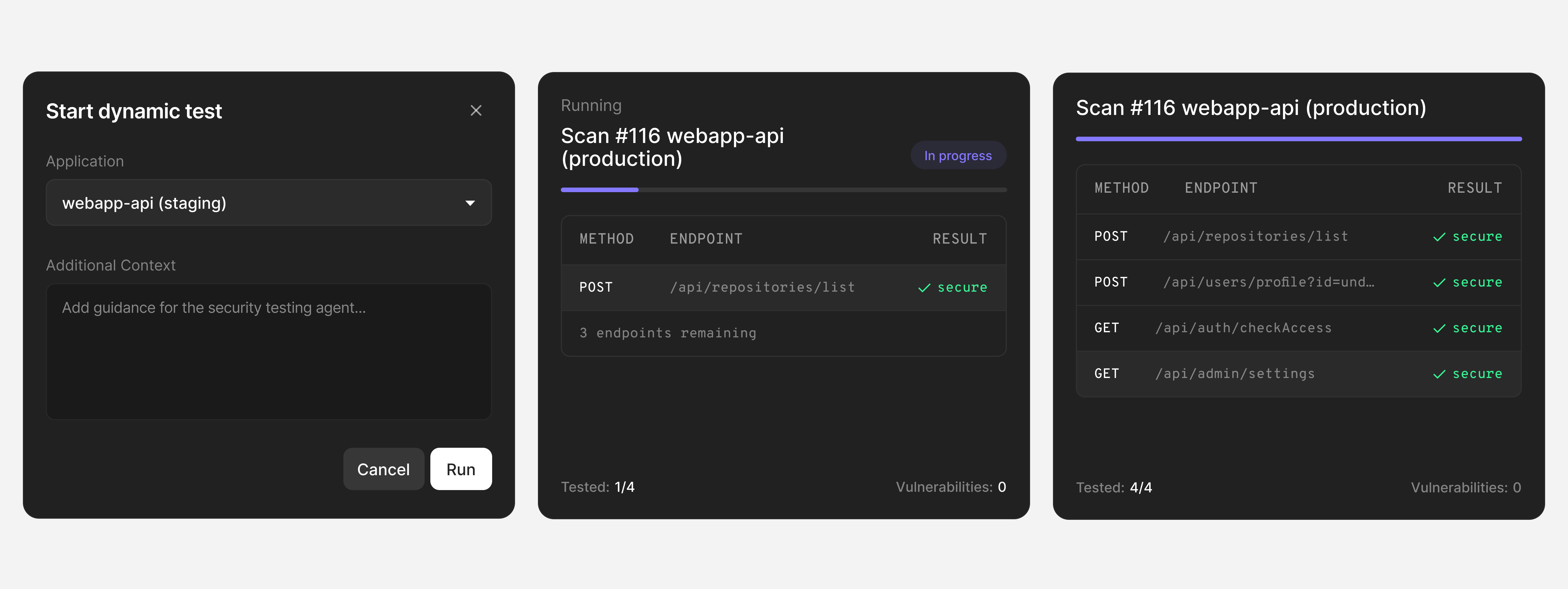
Deploy dynamic testing in three ways. Discover vulnerabilities in your running applications, confirm which findings are exploitable at runtime, and verify that every fix resolves the issue after merge.
-
-
Tests whether users can access data that doesn’t belong to them by modifying object identifiers in real requests and checking for unauthorized responses.
-
depthfirst maps how weak points connect through your application’s data flows and control logic to surface exploitable vulnerability chains.
Discover vulnerabilities in running applications
AI agents authenticate, navigate UI and APIs, and chain requests to execute real attack paths against your running application.
Confirm every finding with proof of exploitability
Findings from code, supply chain, secrets, and infrastructure are tested at runtime. Confirmed vulnerabilities include a unified timeline of static evidence and dynamic exploitation.
Know fixes actually work
depthfirst replays each attack after a fix. A vulnerability is resolved only when the same attack fails in your running application.
Testing modes
Run white-box tests informed by full code context, grey-box tests with partial access, or black-box tests against any URL or API endpoint.
Continuous validation
Dynamic tests re-run automatically after fixes merge, confirming that each vulnerability is resolved at runtime, not just patched in code.
SAST-to-DAST linking
Static findings are linked to dynamic exploitation attempts in a single timeline, showing both the code-level evidence and the runtime result.
Authentication support
Support a wide range of authentication methods and test across multiple scoped roles to reflect real user access.
Secrets & Sensitive Data
Detect and validate credentials across your codebase, CI/CD pipelines, and runtime environments.
Code
Find real vulnerabilities by tracing business logic, data flows, and cross-service interactions across your codebase.
Supply Chain
Trace risk through your full dependency tree and surface only the vulnerabilities with a real execution path to them.